It was quiet weekend and the world was struggling with pandemic recovery when the logging java application in some game server showed a surprising hive of activity which shouldn’t have occured.
Welcome to the cluster bomb of log4j which should have just done logging for java applications but instead , raised a whole of security vulnerabilities that most admins and DevOps people are still struggling to fix.
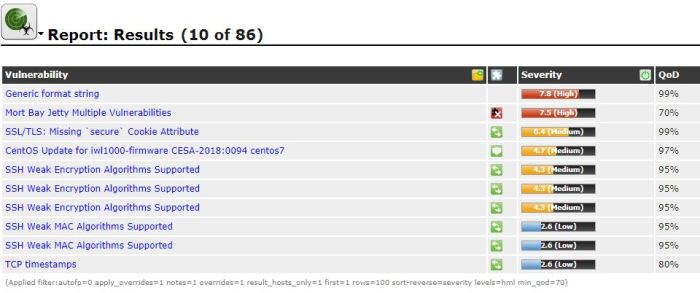
The case so far have following vulnerbilities raised
CVE-2021-44228 :
Apache Log4j2 2.0-beta9 through 2.15.0 (excluding security releases 2.12.2, 2.12.3, and 2.3.1) JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints. An attacker who can control log messages or log message parameters can execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled. From log4j 2.15.0, this behavior has been disabled by default. From version 2.16.0 (along with 2.12.2, 2.12.3, and 2.3.1), this functionality has been completely removed. Note that this vulnerability is specific to log4j-core and does not affect log4net, log4cxx, or other Apache Logging Services projects.
Now as per the mitigation steps provided by Apache here you either upgrade to version 2.17 or above or delete the JNDIlookup class file from the log4j jar file.
As easy it sounds upgrading to latest version of log4j core has its own issue API compatibilty. You from version 2.10.x onwards the api’s have changed , so anyone upgrading directly from 2.1 or 2.2 to 2.17 will definitely face issue in functionality of their applications or webservices.
So its better to remove the JNDI lookup class for those versions ( And also for latter versions )
Now I have see some smart ass admins directly deleting the log4j-* files which will have other unintended consequence of applications crashing due to unavailable jar files
So better to run the following commands
zip -q -d $(find ./ | grep log4j-core ) org/apache/logging/log4j/core/lookup/JndiLookup.class
Update 1: it seems even though the steps are valid at the time of my publishing this, since its an ongoing CVE and more mitigation steps are coming, Apache has already update various versions of log4j with a fix so we do have a version 2.3.2 updated for Java 6 for the older versions of log4j (less than 2.10.x)